As we know that a data breach means leaking of emails addresses and passwords to an untrusted environment. Other terms for this phenomenon include data leak. Therefore, 773 million including E-mail ID’s and 21 million Passwords was leaked. It was published by security researcher Troy Hunt.
Therefore, it was collected from a number of breaches and uploaded to popular cloud service MEGA. The platform has since removed the data, which was promoted on popular hacking forums. However, the massive collection has since been removed from the platform.
According to Hunt, There was collection named “Collection #1”, includes over 12,000 separate files and is more than 87GB in size. It contained 772,904,991 email addresses and 21,222,975 passwords, allegedly from many legitimate breaches that Hunt recognizes in that list. This data leak goes to show that no one should be reusing their old passwords for new services. If you are, now is the time to change that.
Highlights of Data Breach:-
- More than 773 million E-mail ID’s leak.
- More than 21 million passwords leak.
- Information was uploaded to MEGA cloud services.
- The list includes log-in credentials from more than 2,000 websites.
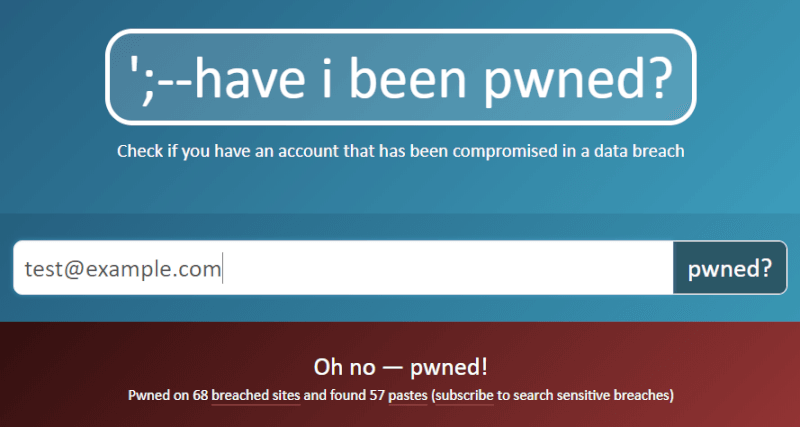
Data Breach: Checking Email Addresses and Passwords in HIBP.
You can check if your email, password, or other data appears on the list for free through his site. Hunt said even his own data appeared on the website. Large breaches like these are often used for “data-stuffing attacks”.
Therefore, hackers use bots to automatically test millions of emails and password combinations across many websites. This means if you use the same password across different websites, you could be at risk of being compromised, even at sites that weren’t hacked. Therefore, users should change their password for the different website for low risk of data leak.
That’s all for today. Stay Tuned To TechBurner For More News.